Prepare for MFA Enforcement for All Employee Users
This article addresses MFA requirements for users without privileged or admin permissions, as defined in “Who’s Affected”). While privileged users and admins are required to use phishing-resistant MFA, Salesforce strongly recommends that all users adopt phishing-resistant MFA methods (security keys and built-in authenticators), to ensure the highest level of protection against identity-based threats.
For more info on the roadmap of upcoming targeted Security changes for the Salesforce Platform, see: Security-Related Product Updates to the Salesforce Platform.
What’s Changing
Salesforce is enforcing Multi-Factor Authentication (MFA) for all employee logins, including direct UI and Single Sign-On (SSO), across both production and sandbox orgs.
Supported MFA verification methods in Salesforce are categorized by their security strength:
-
Phishing-Resistant MFA (Recommended): The most secure and seamless experience. This includes Built-in Authenticators (e.g.,Touch ID, FaceID, Windows Hello) and Security Keys (e.g.,YubiKey from Yubico and the Titan Security Key from Google). We highly recommend adopting Passwordless login via Passkeys to provide users with the fastest and most secure authentication flow available.
-
Standard MFA: Includes the Salesforce Authenticator mobile app and third-party TOTP Authenticator Apps.
Why Is Salesforce Making This Change?
To increase security and better protect your org, Salesforce is moving toward a stronger baseline by technically enforcing MFA for all employees. This change helps to mitigate account takeover (ATO) risks stemming from stolen credentials, credential stuffing, and phishing.
When Does This Change Take Effect?
- Sandboxes: Starting June 22, 2026, staggered over approximately 7 days.
- Production: Starting July 20, 2026, staggered over approximately 30 days
Who’s Affected?
This change affects all users logging into Salesforce (direct UI or SSO logins) in production or sandbox orgs who meet the following conditions:
-
Any user who does not possess any one of these privileges: System Administrator profile, Modify All Data, View All Data, Customize Application, or Author Apex. Note: Users with these privileges are subject to stricter Phishing-Resistant MFA requirements.
Who’s Not Affected?
Users who meet these criteria are already compliant, or exempt, and will experience no change:
-
Experience Cloud or Experience Site Logins are not forced to use MFA, and continue to be an optional setting configurable by org Admins.
-
Direct UI logins where users have a registered MFA verifier already and either the user is assigned the "Multi-Factor Authentication for User Interface Logins" permission or where the org setting “Require multi-factor authentication (MFA) for all direct UI logins to your Salesforce org” is active.
-
SSO logins where users whose SSO IdP already successfully passes a standard MFA or phishing-resistant MFA signal (AMR/ACR) to Salesforce.
Note for SSO logins, we rely on the customer’s Identity Provider (IdP) sending industry standard signals in the ID token or SAML response: ACR (Authentication Context Class Reference) and AMR (Authentication Methods Reference, RFC 8176).
What to Expect
Administrative & Policy Changes
-
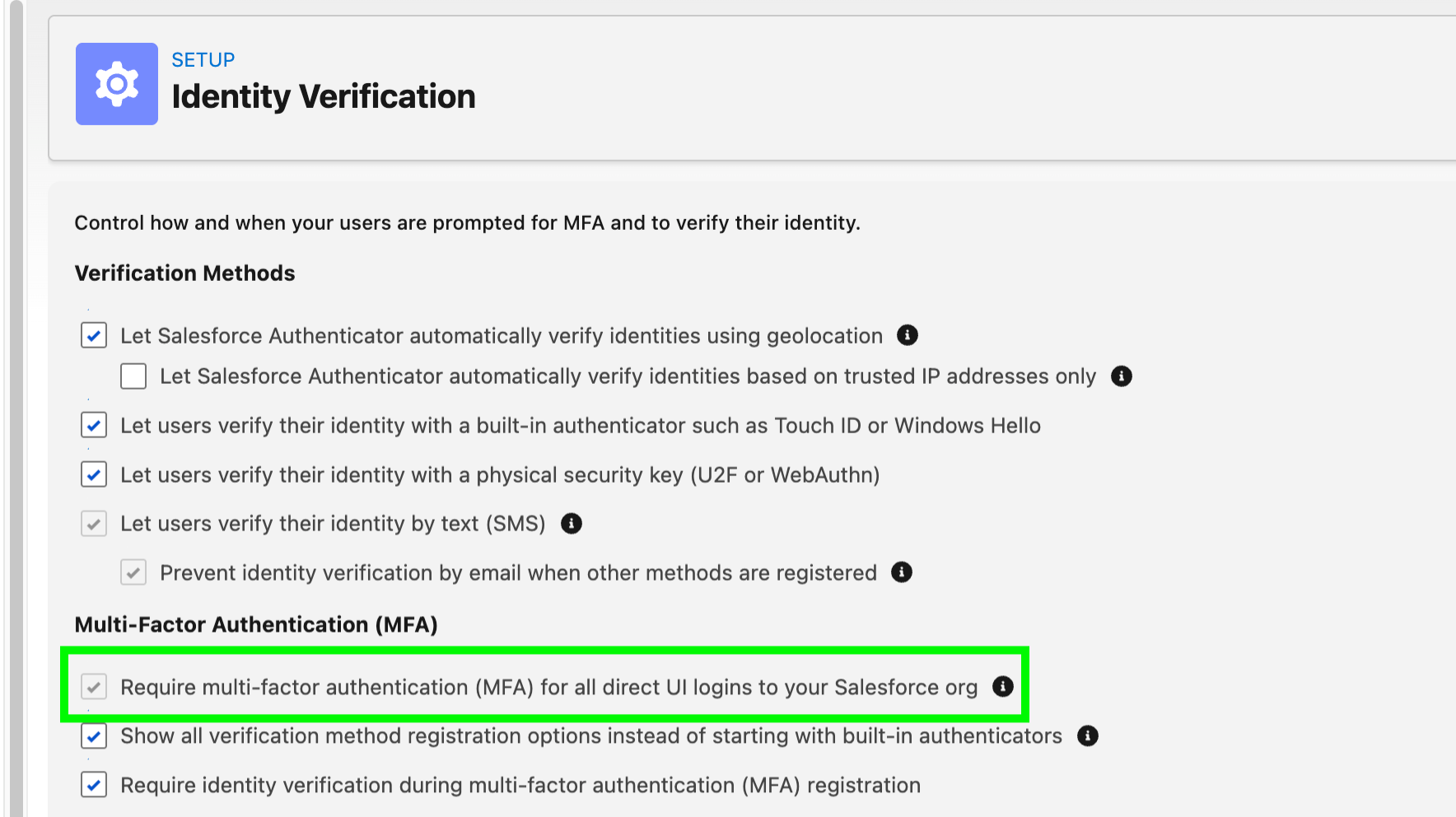
Enforcement of Org-Wide MFA Setting: “Require multi-factor authentication (MFA) for all direct UI logins to your Salesforce org” setting becomes active, and Admins will no longer have the ability to deselect or disable it.
-
Impact to MFA Exemptions: The "Waive Multi-Factor Authentication for Exempt Users" permission will no longer automatically exempt users from MFA. After this change, users with this permission will be prompted to enroll and use an MFA verifier at login. To restore this exemption for valid use cases (e.g., automated testing tools), you must contact Salesforce Support for approval.
-
Trial Org Transition: Trial Orgs converted to a subscription will no longer be given a 30 day grace period for the MFA requirement.
User Login & Registration Experience
-
Direct UI Logins: users will be prompted to enroll a supported MFA verifier if they haven’t previously enrolled, and for all subsequent logins complete the MFA challenge to log in.
-
Enhanced "Passwordless" Login: The login.salesforce.com and My Domain pages will be updated to enable users to enter their username without a password. This change streamlines the user experience for users who log in with a passkey (built-in authenticator or security key) instead of a password. Test automations that use UI logins may need to be updated. Also note upcoming changes to the login experience in September.
-
Phishing-Resistant Defaults: When users are required to register a new MFA method, they will be prompted to register a Passkey (Built-in Authenticator or Security Key which are phishing-resistant options). Users that do not require a phishing-resistant MFA option will have the option to choose third party authenticator apps.
-
In-app Banner reminders will be shown to all users where:
-
Single-Sign-On (SSO) is configured or
-
“Require multi-factor authentication (MFA) for all direct UI logins to your Salesforce org” setting is disabled, or
-
“Waive Multi-Factor Authentication for Exempt Users" permission is assigned, or
-
Security Keys and Built-in Authenticators verifiers are not made available to users.
-
Single Sign-On (SSO) & Integration Requirements
-
SSO Requirements: SSO users whose identity provider does not transmit a valid AMR (Authentication Methods Reference) or ACR (Authentication Context Class Reference) signal will be required to enroll an MFA verifier in the Salesforce UI.
-
OAuth Web Server & Hybrid Token Flows: Connected Apps or External Client Apps using these flows require users to log in to the Salesforce UI to complete OAuth authorization, this login is subject to MFA enforcement. Apps using JWT Bearer or Client Credentials flows are unaffected, as no UI login is required.
Determining Authentication Strength & The Evaluation Logic
Authentication Strength Tiers
Salesforce evaluates every login based on its strength. Whether you log in directly to Salesforce or use a Single Sign-On (SSO) provider, your authentication is categorized into one of three tiers: Phishing-Resistant MFA, Standard MFA, or Weak MFA / No MFA, based on the login method (Salesforce as IdP or other SSO IdP) and what are the specific verifiers or signals present. The classification depends on whether you log in directly (Salesforce as IdP) or via SSO.
|
Tier |
Direct Salesforce Login (Salesforce MFA verifiers) |
SSO (AMR/ACR Signals from your Provider) |
Result |
|
Phishing-Resistant MFA (Recommended) |
Security Keys (WebAuthn), Built-in Authenticators (Touch ID, Windows Hello) |
cert, fido, fido2, fpt, hwk, iris, pin, pki, pop, retina, sc, Smartcard, swk, TLSClient, user, vbm, wia, X509 |
Successful login |
|
Standard MFA |
Salesforce Authenticator, TOTP Apps (Google/Microsoft Auth), Admin Generated Temporary Verification CodesTemp Codes |
Face, mobiletwofactorcontract, multipleauthn, okta_verify, passkey, webauthn |
Successful login |
|
Weak MFA / No MFA |
No MFA |
pwd, sms, tel, email |
Login blocked until enrollment and use of standard MFA verifiers |
These values are subject to change.
Before Enforcement: How to Prepare
-
Audit MFA Configurations and Users:
-
Verify the “Require multi-factor authentication (MFA) for all direct UI logins to your Salesforce org” setting status, and identify users with direct MFA permissions (via Profiles/Permission Sets).
-
Identify all users assigned the "Waive Multi-Factor Authentication for Exempt Users" permission. Because the effect of this permission will be disabled when the change is enforced, you must contact Salesforce Support to retain the exemption for valid use cases (e.g., automated testing tools).
-
-
Set Up Org Verification Options: Define the allowed MFA methods for your users and establish how they choose a method during initial registration.
-
Note: Salesforce requires Privileged Users including Admins users to use phishing-resistant MFA, which means that you must enable built-in authenticators or security keys. Once you enable these methods in Setup, they will be available for all org users. There is no ability to restrict their use to only admins.
-
[Recommended] Activate Passkeys: Enable faster, phishing-resistant logins by toggling on "Allow passwordless login with passkeys" in Identity Verification settings. Users can fulfill this requirement by logging in with just their username and a passkey, such as a built-in authenticator or security key. See Passwordless login using Passkeys.
-
-
Establish Access Recovery Procedures: Define internal processes for Admins to resolve login issues (e.g., generating temporary identity verification codes) to prevent reliance on Salesforce Support for routine resets. See Resolve MFA Access Issues for Your Users.
-
Configure SSO for MFA Compliance: You have two primary paths for SSO: either update your Identity Provider (IdP) to require standard MFA authentication and transmit the necessary AMR/ACR signals, or you may enable Salesforce MFA for your SSO logins. If leveraging your IdP’s MFA service, confirm that the ID token (for OpenID Connect) or the SAML response includes the required AMR/ACR signals.
-
Confirm OIDC AMR signals by reviewing Login History.
-
As SAML ACR values are not yet recorded in Login History (planned for a future release), use a third-party SAML tracer to inspect responses. Note that while the Salesforce SAML Validator assesses AMR/ACR claims, it currently only classifies them as "strong" or "weak" and has not yet been updated to reflect the specific "weak," "standard," and "phishing-resistant" authentication signal strength tiers definitions introduced by this change.
-
-
Pre-Register Users: Proactively communicate the timeline to your users and encourage them to register their MFA methods before the enforcement date to avoid login disruptions. See Register an identity verification method
-
Test Your MFA Implementation: Enable MFA in a sandbox first to validate your configuration, and the user registration flow before the changes reach production. See Test Your MFA Implementation for Salesforce Orgs.
After Enforcement: Resolve Errors
The steps below resolve errors caused by the change.
-
Identify Blocked Users: Monitor login history for users unable to enroll in Salesforce MFA or complete their MFA challenge. Utilize your MFA Support & Access Recovery Procedures (e.g., for locked-out users, Admins can generate a one-time login code), and reference the Common Multi-Factor Authentication (MFA) Troubleshooting for additional help
-
SSO Signal Issues: If your SSO provider is using phishing-resistant MFA or standard MFA authentication, but doesn't pass required signals, you will be required to enroll in Salesforce MFA. To prevent prompts within Salesforce, coordinate with your SSO provider to ensure the ACR or AMR signals are correctly transmitted.
-
Contact Salesforce Support: If an admin is locked out and no other admins are available, contact Salesforce Support for a one-time login code.
Common Questions
How are API logins affected?
This change targets UI-based employee logins only
How are logins via the Salesforce mobile app on Salesforce Mobile SDK logins affected?
-
In Mobile SDK version 13.2.0 and earlier, the default Mobile SDK authentication mode (WebView) cannot support Phishing resistant MFA mechanisms such as Security keys. Users who choose security keys as their MFA option will be blocked from logging in and it is required that their organization pre-configures advanced authentication in the My Domain settings and they use the my domain as their login server. This applies to all the Salesforce internal and third party apps using Mobile SDK. Additionally, Salesforce Mobile App users can use the "Login with Email" option.
-
Login UX Change for all users: Accompanying the phishing-resistant MFA requirement, Salesforce is changing the login flow so that it displays the username field first, then the password or passkey field after the user clicks Log In. This change works with existing Mobile SDK apps, which means it does not require code changes. However, the two-step flow requires updates to existing automated tests that are configured to handle the previous flow.
How do I check if the change has taken effect for my org or instance?
“Require multi-factor authentication (MFA) for all direct UI logins to your Salesforce org” is active and greyed out.
Does MFA now apply to sandbox orgs, not just production?
Yes. With these changes, Salesforce is requiring MFA for all employee (internal) users logging into both production and sandbox orgs. This is a change from prior MFA requirements, which excluded sandboxes.
Does MFA apply to Experience Cloud / Community users?
No. The MFA login requirement applies to employee (internal) users only. Experience Cloud and Community users are not subject to the same MFA login mandate.
We already enforce MFA through our SSO provider (e.g., Okta, ADFS, Entra). Do we still need to configure Salesforce MFA?
SSO logins can satisfy the Salesforce MFA requirement — but only if your identity provider (IdP) sends valid AMR (Authentication Methods Reference) or ACR (Authentication Context Class Reference) signals proving MFA was used. By default, all SSO logins are treated as having no MFA until a recognized phishing-resistant MFA or standard MFA signal is received. If Salesforce cannot detect a valid signal from your IdP, users will be prompted to enroll in Salesforce MFA
Which MFA signal values are recognized by Salesforce from an SSO provider?
Salesforce categorizes SSO MFA strength into three distinct tiers:
-
Phishing-Resistant MFA: cert, fido, fido2, fpt, hwk, iris, pin, pki, pop, retina, sc, Smartcard, swk, TLSClient, user, vbm, wia, X509
-
Standard MFA: Face, mobiletwofactorcontract, multipleauthn, okta_verify, passkey, webauthn
-
Weak / No MFA (default): pwd, sms, tel, email
If phishing-resistant MFA or standard MFA signals are detected, the user gains access immediately with no additional authentication requirements.
However, if Weak / No MFA signals are received then the user will then be prompted via the Salesforce UI to select a verification method and link it to their Salesforce account.
Can we still use the "Waive Multi-Factor Authentication for Exempt Users" permission?
After the enforcement date, this permission will no longer automatically waive MFA requirements. Users with this permission will be prompted to enroll and use MFA in the Salesforce UI. To restore the exemption for valid use cases (e.g., automated testing tools), you must contact Salesforce Support for approval.
What if a user or admin gets locked out?
If a user is locked out, their org Admin can generate a temporary identity verification code, disconnect old verification methods, and assist with re-registration. See Resolve MFA Access Issues for Your Users (Salesforce Orgs). If an Admin is locked out and no other administrators are available, contact Salesforce Support for a one-time login code..
Change Log
|
Date |
Change |
|
May 5, 2026 |
Initial publication |
005321561