You are here:
Data Encryption Keys (DEKs)
The Shield Platform Encryption services can use three types of DEK: derived, root key created, or customer supplied. All have AES-256 bit strength. Derived DEKs and DEKs supplied by the customer aren’t persisted, but exist only in the encrypted key cache. Root key created DEKs are wrapped by the root key and stored in the database and unwrapped by the same root key when needed.
Derived DEKs
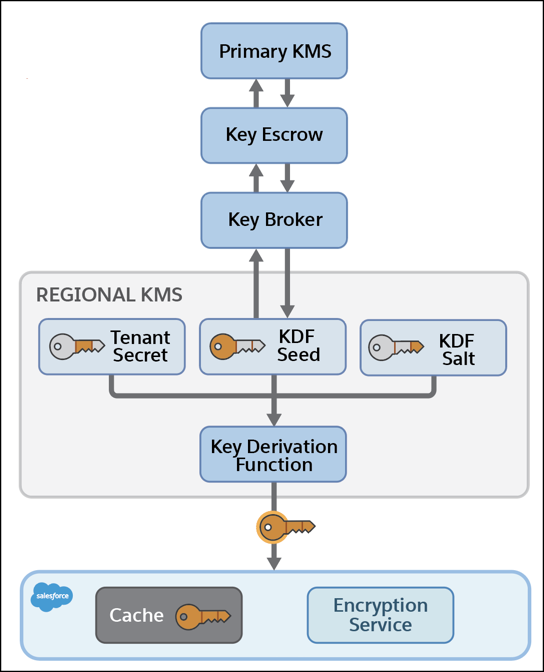
Customer-specific key material for use in derivation is supplied by customers or generated by customers on demand, and then stored securely wrapped in the database. Derived DEKs are generated on demand from the KDF seed and KDF salt secrets generated by the HSM.
The KDF seed and KDF salt are used as inputs to Password-Based Key Derivation Function 2 (PBKDF2) to derive the DEK. PBKDF2 is run on the Shield Key Management Service in a Salesforce data center. Data encryption keys are distributed via the Key Escrow server to the regional Shield KMS and stored in its encrypted key cache. The KDF seed and KDF salt are generated at the start of each Salesforce release and stored securely in the primary KMS. They’re used to derive DEKs on demand.
Customer-Supplied DEKs
Customers who opt out of key derivation (for BYOK or Cache-Only Keys) generate the DEK outside of Salesforce. The DEKs are supplied to Shield Platform Encryption through a secure channel (TLS). Or, they can be fetched on-demand from a customer-specified external key management service.
- For BYOK, the DEKs are wrapped and stored in the database until needed. Then they’re unwrapped by the regional Shield KMS or External KMS and placed in the encrypted key cache.
- For Cache-Only Keys, the DEKs are injected directly into the encrypted key cache.
Root Key Wrapped DEKs
For those services that use root keys, such as Search encryption, the customer first generates a root key in the regional Shield KMS or in an external KMS. When the root key is active, the customer triggers generation of a DEK, also within a KMS. The KMS then uses the root key to wrap the DEK. The wrapped DEK is sent back to the application or service that requires the DEK, and it’s stored in the Salesforce database until needed. When needed, the DEK is sent to the issuing KMS and unwrapped using the root key. Then the unwrapped DEK is returned to the application over a secure channel and stored.

