You are here:
Create a Native Single Sign-On Experience in Your App
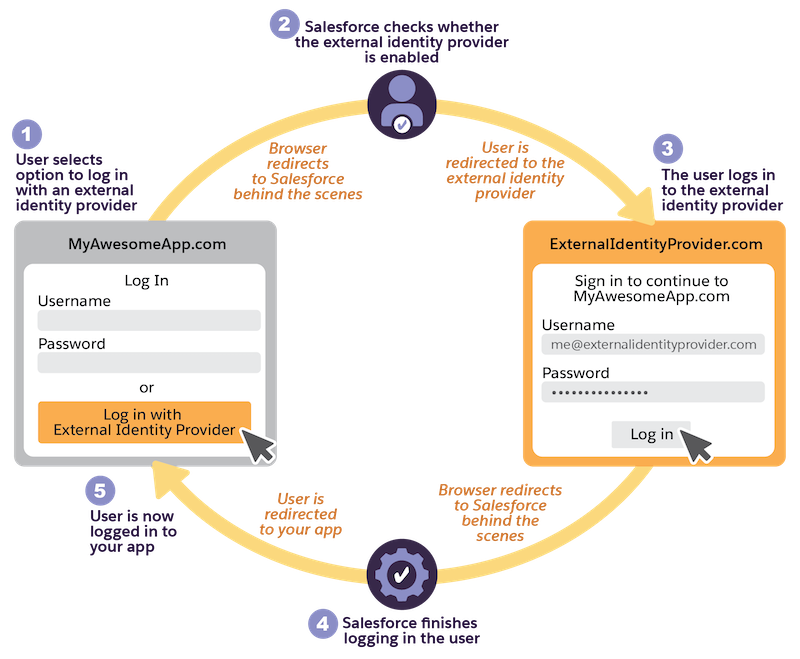
With an optional parameter in the OAuth 2.0 web server flow and user-agent flow, you can build a single sign-on (SSO) experience that feels like your third-party app is integrated with an external identity provider. With this process, you link an OAuth flow to an SSO flow while maintaining control of the experience within your app. This parameter is supported for Experience Cloud sites, so you can use this capability to add SSO to a Headless Identity implementation. This parameter is also supported for My Domain.